You can Download Chapter 15 Networking Concepts Questions and Answers, Notes, 2nd PUC Computer Science Question Bank with Answers Karnataka State Board Solutions help you to revise complete Syllabus and score more marks in your examinations.
Karnataka 2nd PUC Computer Science Question Bank Chapter 15 Networking Concepts
2nd PUC Computer Science Networking Concepts One Mark Questions and Answers
Question 1.
What is networking?
Answer:
- A computer network is a group of autonomous computers that are connected to each other for the purpose of communication.
- A computer network allows the sharing of resources and information among devices connected to the network.
Question 2.
What is the server?
Answer:
A server is a computer program that provides services to other computer programs (and their users) in the same or other computers. The computer that a server program runs in is also referred to as a server.
Question 3.
What is the client?
Answer:
The client is a user or a software who makes a request to the server.
A client is the requesting program or user in a client/server relationship.
![]()
Question 4.
What is topology?
Answer:
It is the geometric arrangement of a computer system in a network. Common topologies include a linear bus, star, ring and ring.
Question 5.
Expand 2G.
Answer:
The expansion of 2G is ‘second generation’.
Question 6.
What is a virus?
Answer:
A computer virus is a computer program that is able to .copy all or part of its code into other programs or files. They perform malicious or harmful processes such as deleting or changing files.
Question 7.
What is chatting?
Answer:
It is online communication between two users through the computer. Once a chat has been initiated, either user can enter text by typing on the keyboard and the entered text will appear on the other user’s monitor.
Question 8.
What is cyber law?
Answer:
The cyber law has been referred to as the Law of the Internet. Cyberlaw is the part of the overall legal system that deals with the Internet, cyberspace, and their respective legal issues.
Question 9.
What are cookies?
Answer:
Cookies are small messages webserver transmit to a web browser.
A cookie is an HTTP header that consists of text-only data saved on your computer. Cookies are used by Web sites to keep track of their visitors.
![]()
Question 10.
What are hackers?
Answer:
Any individual who illegally breaks into computer systems to damage or steal information.
2nd PUC Computer Science Networking Concepts Two Mark Questions and Answers
Question 1.
List the goals for networking.
Answer:
The goals of networking are resource sharing, reliability, cost factor, and communication medium.
Question 2.
What do you mean by transmission modes?
Answer:
The way in which data is transmitted from one place to another is called data transmission mode. It indicates the direction of the flow of information.
Question 3.
Which are the switching technology used?
Answer:
The different switching technology is Circuit Switching, Packet Switching, and Message Switching.
![]()
Question 4.
What is a SIM card?
Answer:
A Subscriber Identity Module (SIM) card is a portable memory chip used mostly in cell phones. These cards hold the personal information of the account holder, including his or her phone number, address book, text messages, and other data.
Question 5.
What is network security?
Answer:
A specialized field in computer networking that involves securing a computer network infrastructure. It consists of the provisions and policies to prevent and monitor unauthorized access, misuse, modification, and network-accessible resources.
Question 6.
What are the advantages of EDGE?
Answer:
EDGE (Enhanced Data GSM Environment) is a faster version of GSM designed to deliver data at rates up to 384 Kbps and enable the delivery of multimedia and other broadband applications to mobile phone and computer users.
2nd PUC Computer Science Networking Concepts Three Mark Questions and Answers
Question 1.
Explain the HTTP.
Answer:
HTTP is a set of standards that allow users of the World Wide Web to exchange information found on web pages. HTTP defines how messages are formatted and transmitted, and what actions Web servers and browsers should take in response to various commands. For example, when you enter a URL in your browser, this actually sends an HTTP command to the Web server directing it to fetch and transmit the requested Web page.
Question 2.
Classify and explain servers.
Answer:
A server is a computer program that provides services to other computer programs (and their users) in the same or other computers. The computer that a server program runs in is also referred to as a server.
Servers can be broadly classified into Dedicated servers and Non-dedicated servers.
1. Dedicated servers:
A computer exclusively reserved for the server’s job and its only job is to help workstations to access data, software and hardware resources. The term “dedicated server” can also mean a single computer within a network that is reserved for a specific purpose.
For example, within a network, you could have a computer dedicated to printer resources, another computer dedicated to Internet connections, another computer serving as a firewall, etc. These computers would all be dedicated servers, as the whole computer is allocated for a specific task within the network.
2. Non-dedicated servers:
A computer in a network acts as a server as well as a workstation is called a non-dedicated server. It is server upon which applications are available, and also network management software runs in the background. Non-dedicated servers are common in peer-to-peer networks. A peer to peer network is a network without a dedicated server. It is composed entirely of workstations that can be set up to share some of their services, like printers or files. These computers require more memory and work slower. It is suitable for small networks.
![]()
Question 3.
Explain the types of networking.
Answer:
A local Area Network (LAN) is a computer network covering a small physical area, like a home, office, or small group of buildings, such as a school, or an airport.
The characteristics of LANs:
- LAN’s enable the sharing of resources such as files or hardware devices that may be needed by multiple users
- Is limited in size, typically spanning a few hundred meters, and no more than a mile
- It is fast, with speeds from 10 Mbps to 10 Gbps.
- Requires little wiring, typically a single cable connecting to each device
- Has lower cost compared to MAN’S or WAN’s LAN’s can be either wired or wireless Twisted pair, coaxial or fiber optic cable can be used in wired LAN’s.
- Every LAN uses a protocol -a set of rules that governs how packets are configured and transmitted.
- Nodes in a LAN are linked together with a certain topology. These topologies include: Bus, Ring, Star
- LANs are capable of very high transmission rates (100s Mb/s to G b/s)
Metropolitan area network:
A metropolitan area network (MAN) is a network that connects two or more local area networks together but does not extend beyond the boundaries of the town/city.
- A MAN is covers larger geographical area than a LAN, ranging from several blocks of buildings to entire cities.
- A MAN might be owned and operated by a single organization, but it usually will be used by many individuals and organizations.
- A MAN often acts as a high speed network to allow sharing of regional resources.
- A MAN typically covers an area of between 5 and 50 km diameter.
- Examples of MAN: Telephone company network that provides a high-speed DSL to customers and cable TV network.
Wide area network:
A wide area network (WAN) is a computer network that covers a broad area. The largest and most well-known example of a WAN is the Internet. A WAN is a data communications network that covers a relatively broad geographic area (i.e. one city to another and one country to another country).
- To cover great distances, WANs may transmit data over leased high, speed phone lines or wireless links such as satellites.
- Multiple LANs can be connected together using devices such as bridges, routers, or gateways, which enable them to share data.
- It operates on a low data transfer rate
Question 4.
Which are the networking techniques?
Answer:
The networking techniques (topologies) are Bus topology, Ring topology, Star topology, Three topology, Mesh topology, Extended star topology.
Question 5.
Explain the cables and different types of cables used in transmission?
Answer:
The cables are said to be transmission media or communication channels of the network. The cables are used to connect two or more computers in the network.
Network Cables:
- Unshielded Twisted Pair Cable (UTP cable)
- Shielded Twisted Pair (STP) cable
- Coaxial Cable
- Fiber Optic Cable
Twisted-Pair Wire – The cable has four pairs of wires inside the jacket. Each pair is twisted with a different number of twists per inch. They are used for both voice and data transmission. Cat 1 to Cat 5 is the different categories and the RJ-45 connector is used to connect a cable.
Coaxial Cable – Coaxial cabling has a single copper conductor at its center. A plastic layer provides insulation between the center conductor and a braided metal shield. Transmission speed range from 200 million to more than 500 million bits per second.
Fiber Optics – Fiber optic cabling consists of a center glass core surrounded by several layers of protective materials. It transmits light rather than electronic signals eliminating the problem of electrical interference. Transmission speed could go up to as high as trillions of bits per second.
![]()
Question 6.
List the differences between simplex, half-duplex and full-duplex.
Answer:
The differences between simplex, half-duplex and full-duplex are
| Simplex | Half-duplex | Full duplex |
| communication occurs in one direction only | Communication in both directions, but only one direction at a time (not simultaneously). | It allows communication in both directions simultaneously. |
| Radio Receiver and Radio Transmitter | walkie-talkie | Telephone networks are full-duplex |
Question 7.
Explain the applications of networking.
Answer:
SMS (Short Message Service), commonly referred to as “text messaging,” is a service for sending short messages of up to 160 characters (224 characters if using a 5-bit mode) to mobile devices, including cellular phones, smartphones and PDAs.
SMS messages do not require the mobile phone to be active and within range and will be held for a number of days until the phone is active and within range. SMS messages are transmitted within the same cell or to anyone with roaming service capability. They can also be sent to digital phones in a number of other ways, including:
- From one digital phone to another
- From Web-based applications within a Web browser
- From instant messaging clients like ICQ
- From VoIP applications like Skype ‘
- Enhanced messaging service (EMS), an adaptation of SMS that allows users to send and receive ringtones and operator logos, as well as combinations of simple media to and from EMS-compliant handsets.
Users can send messages from a computer via an SMS gateway. SMS gateways are Web sites that allow users to send messages to people within the cell served by that gateway. They also serve as international gateways for users with roaming capability.
1. Chat:
It is online communication between two users through a computer. Once a chat has been initiated, either user can enter text by typing on the keyboard and the entered text will appear on the other user’s monitor. Most networks and online services offer a chat feature.
2. Video Conferencing:
A video-conference (or Video Conference) is a live video connection between people in separate locations for the purpose of communication or interaction. Video-conferencing allows people to communicate visually from anywhere in the world.
There are three main types of video conference solutions for businesses: point-to-point, multipoint and streaming.
- Point-to-point (sometimes referred to as single call) is a direct connection between two locations. It’s like a telephone call, just with video.
- Multipoint lets three or more people or locations take part in the same video conference. Multiple parties can meet through HD video in a meeting room, from a desktop at work, from a home computer, or even over a smartphone or tablet when on the road.
- Streaming connects your video conference to others who may choose to view the meeting on a remote computer or mobile device using software instead of hardware.
2nd PUC Computer Science Networking Concepts Five Mark Questions and Answers
Question 1.
Explain the working of OSI and TCP/IP.
a. OSI reference model:
Answer:
It was created by the International Organization for Standardization (ISO) to provide a logical framework for how data communication processes should interact across networks. Standards were created for the computer industry allowing different networks to work together efficiently.
There are 7 layers in the OSI model. Each layer is responsible for a particular aspect of data communication. For example, one layer may be responsible for establishing connections between devices,
1. Application Layer:
Provides network services to user applications, it is responsible for exchanging information between programs running on the machine, such as an e-mail program, and other services running on a network.
2. Presentation Layer:
Concerned with how data is converted and formatted for data transfer. This layer performs code conversion, data translation, compression, and encryption.
3. Session Layer:
Determines how two devices establish, maintain and manage a connection – how they talk to each other. These connections are called sessions.
4. Transport Layer:
Responsible for breaking the data into segments, establishing an end-to-end logical connection between machines, and providing for error handling.
5. Network Layer:
Responsible for determining addressing on the network, determining the routes that information will take on its journey, and managing network traffic congestion. Data at this level is packaged into packets.
6. Data Link Layer:
It provides the link for how data, packaged into frames are communicated through hardware to be transported across a medium. It communicates with network cards, manages physical layer communications between connecting systems and handles error notification
7. Physical Layer:
Specifies how data is processed into bits and physically transferred over medium, such as cables. It’s responsible for activating and maintaining the physical link between systems.
b. TCP/IP:
TCP/IP stands for “Transmission Control Protocol / Internet Protocol”. It is basically a network protocol that defines the details of how data is sent and received through network adapters, hubs, switches, routers, and other network communications hardware. It was developed by the US department of defense for the purpose of connecting government computer systems to each other through a global, fault-tolerant, network.
It has become the most popular networking protocol throughout the world and well supported by almost all computer systems and networking hardware.
TCP, Transmission Control Protocol, breaks data up into packets that the network can handle efficiently, verifies that all the packets arrive at their destination, and reassembles the data.
IP, Internet Protocol, envelopes and addresses the data, enables the network to read the envelope and forward the data to its destination and defines how much data can fit in a single packet.
After TCP/IP was developed, many more protocols included, Simple Mail Transfer Protocol (SMTP) used for transferring email across the internet, File Transfer Protocol (FTP) used to upload and download files, and HyperText Transfer Protocol (HTTP) the protocol used to .transport web pages.
The TCP/IP model’s protocol layers
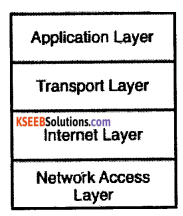
TCP/IP must be responsible for the following tasks:
- Dividing messages into manageable chunks of data that will pass efficiently through the transmission medium.
- Interfacing with the network adapter hardware.
- Addressing:
The sending computer must be capable of targeting data to a receiving computer. The receiving computer must be capable of recognizing a message that it is supposed to receive. - Routing data to the subnet of the destination computer, even if the source subnet and the destination subnet are dissimilar physical networks.
- Performing error control, flow control, and acknowledgment: For reliable communication, the sending and receiving computers must be able to identify and correct faulty transmissions and control the flow of data.
- Accepting data from an application and passing it to the network.
- Receiving data from the network and passing it to an application.
![]()
Question 2.
Explain various networking devices used?
Network Interface Cards
Answer:
The network interface card (NIC) provides the physical connection between the network and the computer workstation. Network interface cards are a major factor in determining the speed and performance of a network. The most common network interface connections are Ethernet cards.
1. Switches:
A switch is a hardware device that provides a central connection point for cables from workstations, servers, and peripherals, switch forwards data only to the port on which the destination system is connected.
Most switches are active, that is they electrically amplify the signal as it moves from one device to another. Switches manage the data flow on the connection, it can send and receive data on the connection at the same time. Switches use three methods to deal with data as it arrives. They are Cut-through, Store-and-forward, and Fragment-free.
2. Repeaters:
Since a signal loses strength as it passes along a cable, it is often necessary to boost the signal with a device called a repeater. The repeater electrically amplifies the signal it receives and rebroadcasts it.
3. Bridges:
Bridges are networking devices that connect networks. Sometimes it is necessary to divide networks into subnets to reduce the amount of traffic on each larger subnet or for security reasons. Once divided, the bridge connects the two subnets and manages the traffic flow between them.
Three types of bridges are used in networks are Transparent bridge, Translational bridge, Source-route bridge.
Most bridges can “listen” to the network and automatically figure out the address of each computer on both sides of the bridge. The bridge can inspect each message and, if necessary, broadcast it on the other side of the network. The bridge manages the traffic to maintain optimum performance on both sides of the network.
a. Routers:
Routers are network devices that route data around the network. By examining data as it arrives, the router can determine the destination address for the data; then, by using tables of defined routes, the router decides the best way for the data to reach a destination. The router can direct traffic to prevent a crash.
b. Hubs:
A network hub contains multiple ports. When a packet arrives at one port, it is copied to all ports of the hub for transmission.
The two types of hubs are active or passive hubs. Active hubs regenerate signal before forwarding it to all the ports and require a power supply. Passive hubs, do not need power and they don’t regenerate the data signal.
c. Gateways:
It is a device that connects dissimilar networks. The term gateway is applied to any device, system, or software application that can perform the function of translating data from one format to another. The key feature of a gateway is that it converts the format of the data, not the data itself. The conversion from one data format to another takes time, and so the flow of data through a gateway is always slower than the flow of data without one.
d. Modems:
The modem is a short form of the terms modulator and demodulator. Modems translate digital signals from a computer into analog signals that can travel across phone lines. The modem modulates the signal at the sending end and demodulates at the receiving end.
Modems provide a relatively slow method of communication. Modems are available as internal devices that plug into expansion slots in a system; external devices that plug into serial or USB ports;
Question 3.
What is topology explain in detail?
Answer:
Topology is the geometric arrangement of a computer system in the network. Common topologies include a
- Linear bus Topology
- Star Topology
- Tree Topology and
- Ring Topology
Linear Bus
A linear bus topology consists of a central cable with a terminator at each end. All nodes (file server, workstations, and peripherals) are connected to the linear cable.
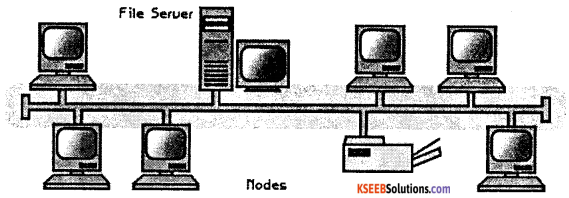
Advantages of a Linear Bus Topology
- Easy to connect a computer or peripheral to a linear bus.
- It requires less cable length than a star topology.
Disadvantages of a Linear Bus Topology
- The entire network shuts down if there is a break in the main cable.
- Terminators are required at both ends of the backbone cable.
- Difficult to identify the problem if the entire network shuts down.
- Not meant to be used as a stand-alone solution in a large building.
star Topology
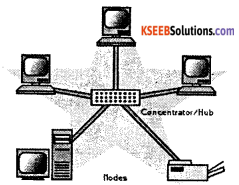
A star topology is designed with each node (file server, workstations, and peripherals) connected directly to a central network hub, switch. Data on a star network passes through the hub, switch, before continuing to its destination. The hub, switch, manages and controls all functions of the network. It also acts as a repeater for the data flow. Advantages of a Star Topology.
- Easy to install and wire.
- No disruptions to the network when connecting or removing devices.
- Easy to detect faults and to remove parts.
Disadvantages of a Star Topology
- Requires more cable length than a linear topology.
- If the hub, switch fails, nodes attached are disabled.
- More expensive than linear bus topologies because of the cost of the hubs, etc.
Tree topology
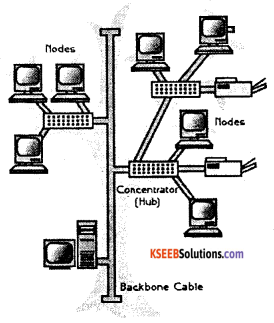
A tree topology combines characteristics of linear bus and star topologies. It consists of groups of star configured workstations connected to a linear bus backbone cable. Tree topologies allow for the expansion of an existing network.
Advantages of a Tree Topology
- Point-to-point wiring for individual segments.
- Supported by several hardware and software venders.
Disadvantages of a Tree Topology
- Overall length of each segment is limited by the type of cabling used,
- If the backbone line breaks, the entire segment goes down.
- More difficult to configure and wire than other topologies.
Ring Topology
In-ring network each node connects to exactly two other nodes, forming a single continuous pathway for signals through each node – a ring. Data travels from node to node, with each node along the way handling every packet.
Advantages
- Very orderly network where every device has access to the token and the opportunity to transmit
- Performs better than a star topology under heavy network load
- Does not require a network server to manage the connectivity between the computers
Disadvantages
- One malfunctioning workstation or bad port in the MAU can create problems for the entire network
- Moves, adds and changes of devices can affect the network
- Much slower than an Ethernet network under normal load.
![]()
Question 4.
What is a gateway? Explain.
Answer:
A network gateway is an internetworking system capable of joining together two networks that use different base protocols. A network gateway can be implemented completely in software, completely in hardware, or as a combination of both. The key feature of a gateway is that it converts the format of the data, not the data itself.
Gateway functionality differs in many ways. For example, a router that can route data from an IPX network to an IP network is, technically, a gateway. The same can be said of a translational bridge that, converts from an Ethernet network to a Token Ring network and back again.
Software gateways can be found everywhere. Many companies use an email system such as Microsoft Exchange. These systems transmit mail internally in a certain format. When email needs to be sent across the Internet to users using a different email system, the email must be converted to another format, this conversion process is performed by a software gateway. In enterprises, the gateway often acts as a proxy server and a firewall. Gateways also associated with router-id switch.
Question 5.
Explain network security in detail.
Answer:
Network security refers to any activities designed to protect network and related activities. It protects the usability, reliability, integrity, and safety of network and data. Good network security identifies a variety of threats and stops them from entering or spreading on network.
The network security concerns with allowing only legal or authorized users and programs to gain access to information resources like databases. It also ensures that properly authenticated users get access only to those resources that they are supposed to use. Many network security threats today are spread over the Internet. The most common include:
- Viruses, worms, and Trojan horses
- Spyware and adware
- Zero-day attacks also called zero-hour attacks
- Hacker attacks
- Denial of service attacks
- Data interception and theft
- Identity theft
A network security system usually consists of many components. Ideally, all components work together, which minimizes maintenance and improves security.
Network security components include:
- Anti-virus and anti-spyware
- Firewall, to block unauthorized access to your network.
- Intrusion prevention systems (IPS), to identify fast-spreading threats, such as zero-day or zero-hour attacks
- Virtual Private Networks (VPNs), to provide secure remote access
The network security makes use of a variety of resources like user name, password, encrypted smart cards, biometrics, and firewalls to protect resources.
Question 6.
Give the measures for preventing the virus.
Answer:
The different measures for preventing virus are
1. Install quality antivirus:
The users should install professional, business-grade antivirus software on their PCs. Pro-grade antivirus programs update more frequently throughout the, protect against a wider range of threats (such as rootkits), and enable additional protective features (such as custom scans).
2. Install real-time anti-spyware protection:
Use of professional (or fully paid and licensed) anti-spyware programs are required to prevent infections and fully remove those infections already present.
3. Keep anti-malware applications current:
Antivirus and anti-spyware programs require regular signature and database updates. Without these critical updates, anti-malware programs are unable to protect PCs from the latest threats. Computer users must keep their antivirus and anti-spyware applications up to date.
4. Perform daily scans:
Enabling complete, daily scans of a system’s on hard drive gives protection. These daily scans can be invaluable in detecting, isolating, and removing infections that initially escape security software’s attention.
5. Disable autorun:
Many viruses work by attaching themselves to a drive and automatically installing themselves. As a result, connecting any network drives, external hard disks, or even thumb drives to a system can result in the automatic propagation of such threats. The users can disable the Windows autorun feature to avoid.
6. Don’t click on email links or attachments:
Users should never click on email attachments without at least first scanning them for viruses using a business-class anti-malware application. As for clicking on links, users should access Web sites by opening a browser and manually navigating to the sites.
7. Use a hardware-based firewall:
The software-based firewall included with Windows isn’t sufficient to protect systems. For this reason, all PCs connected to the Internet should be secured behind a capable hardware-based firewall.